ROC ZTNA
ROC ZTNA or ROC Zero-Trust allows you to control access rules to internal traffic inside the ROC. You can lock down internal servers, IoT devices, computers, laptops, & tablets via our easy to use granular rules.
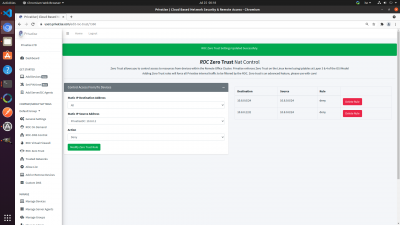
ROC Zero-Trust should look like this:
Granular Access Permissions
By default, all internal traffic is allowed through the ROC. If you want to deny all traffic and then allow specific traffic through, you would:
1. Set a rule to Deny All to All.
2. Then set your specific allow rules.
Allowing Specific Groups
Sometimes you'll want to specify group policies instead of allowing specific devices or servers. In that case, you can scroll down to the specific group. All sub-groups that share a ROC should be visible under control settings.